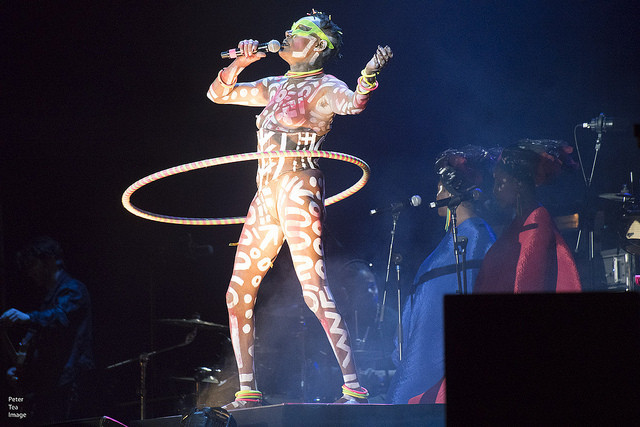
Singer, actress, sulphurous icon of the 80s New York, queen of disco, muse of Andy Warhol … Grace Jones has lived a thousand lives, SBM says.
After twenty years of silence, she released a new album recorded in her home country, Jamaica, in 2008 with reggae legends Sly & Robbie. The public and critical reception was so positive that the pop diva has been touring the world ever since with a spectacular show highlighting her avant-garde look and extravagant headdresses, which continue to work wonder, the casino and hotel operator says.
As part of the Monte-Carlo Sporting Summer Festival 2018, Grace Jones will come to Monaco on August 6 to dance the Libertango on the stage of the Salle des Etoiles.
Tickets are on sale at €300, including dinner. Info on montecarlolive.com.
READ ALSO
Princess Charlene kicks off Princess Grace Awards with Paramount Pictures tribute event